Advanced Security: Marking AWS WAF’s Homework
The same security scenarios are checked thoroughly. Privilege escalation, SQL injection, Port scanning and so on. These checks form the bedrock of defensive security, but as…
The evolution of Security Information and Event Management (SIEM) is deeply intertwined with cloud computing, both in terms of technological breakthroughs the cloud provided and from its inherent security challenges.
With the rise of cloud computing, we no longer rely on long-lived resources. An ephemeral infrastructure obscures the identity of the components and, even if you do have the visibility it doesn’t necessarily mean you can comprehend the meaning behind the components. In fact, with containers and functions being an integral part of modern cloud-native applications the visibility is now even harder.
The cost, in particular of the network and bandwidth, also creates an unexpected security challenge. With on-premise infrastructure, there is no need to pay to mirror network traffic (required to monitor) but, in contrast, public cloud providers charge a hefty sum for this functionality. As an example, in AWS you pay for each VPC mirroring session and also for the bandwidth going from the mirror to the monitoring system.
Raising logging and metric data costs put pressure to collect fewer data and has a negative impact on the effectiveness of the security monitoring solution because it’s almost impossible to predict what the future needs of an investigation will be. On the other hand, the technical ability to properly scale using cloud and ingest more data had a tremendous positive impact.
However, even that ended up creating analyst fatigue, with most SIEMs having low satisfaction rates due to false positives.
The scalability of public cloud, combined with gross misconfigurations and over-exposure of resources to the internet, also widens the scope of attacks and security threats. Today, advanced persistent threats (APT), ransomware and geo-distributed Denial of Service (DDoS/DDoD) attacks among many other security issues pose real peril to organizations of any size. The need for proper enterprise detection and response capabilities and services is vital to tackle the cloud security challenges, and a good SIEM solution is one of the best weapons you can get.
The term Security Information and Event Management (SIEM) is not new but, during the last few years has become incredibly popular.
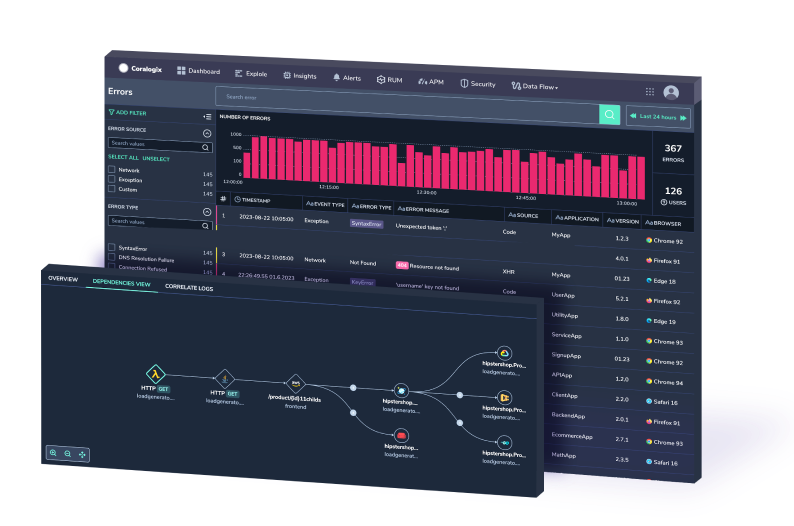
The concept behind it is rather simple yet ambitious, a SIEM solution collects and analyzes events – in both real-time and by looking back at historical data – from multiple data sources within an organization to provide capabilities such as threat detection, security incident management, analytics and overall visibility across the systems in an organization.
SIEM-like systems have existed for several years but it was only in the early 2000s that the term really came to life. At the time, cloud computing was practically non-existent with only some providers giving first steps in the domain.
The first generation of SIEM was then fully on-premise, incredibly expensive and suffering from huge problems related to data source integrations and mostly scalability (vertical was the only way to go) without being able to properly cope with ever-growing amounts of data.
With the rise of cloud computing popularity and maturity, also SIEM solutions evolved and were able to benefit from it. The second generation of SIEM solution was then born and being able to leverage those technology advancements, such as near-unlimited growth storage capacity and elastic computing resources, the scalability limitations were then solved by enabling growth to happen horizontally and therefore coping with the constant data growths.
However, a new problem emerged: too much data. Security professionals and engineers using SIEM solutions became drowned with so much information that it became hard to find and understand what was actually relevant. A next-generation of SIEM solutions started to appear with focus on the operational capabilities and properly leverage analytics & machine learning algorithms to find those needles in the haystack.
The new generation of SIEM effectively enables teams to gain meaningful visibility over the infrastructure and take relevant actions.
Even people without a security background are now able to use a modern SIEM solution. The dashboards, alerts and recommended actions are now made to be comprehensive, straightforward and user friendly, while still enabling security professionals to leverage forensic capabilities within the solution if needed.
When looking for a SIEM solution, you should obviously look for one that can truly cope with data growth, and cloud-based managed solutions are naturally a good fit for this, but scalability by itself is not enough. One aspect to keep in mind is the data optimization capability, such as the ability to process log insights without actually retaining the log data which is a prime example of a key functionality that enables massive cost savings in the long run.
Without data, a SIEM is rendered useless and, with the current wide technology landscape is becoming incredibly hard to connect to all the existing data sources within an organization. Having good ready available integration capabilities with 3rd party software & data sources is important functionality to take into account. The value of SIEM comes from being able to correlate events (e.g. network traffic) with applications, cloud infrastructure, assets, transactions, and security feeds.
In the end, you want to get as much visibility and insights as possible into your cloud infrastructure by relying on raw traffic data (e.g. using traffic mirroring), because that enables you to detect anomalies such as advanced persistent threats (APT’s) without the attacker even noticing it. Raw network traffic data capture and deep packet inspection is something that one might often overlook.
Normally, web server logs wouldn’t contain the actual data (payload) sent to the server (e.g. database). For example, if someone sends a malicious query containing a SQL injection, it will go unnoticed unless your SIEM solution is capable of capturing and inspecting that raw data.
While the collection and correlation of the information you have within the organization – especially network traffic events – is the most important data point for a SIEM solution, quite often it is not enough to reason only with that data in a manner that can provide actionable intelligible alerts and recommendations.
A SIEM solution should be capable of enriching the organization’s data with additional relevant information. The techniques may vary, but some of the obvious ones are to extract the geolocation of IP addresses, detect suspicious strings that may indicate usage of Domain Generation Algorithms (DGA), public information regarding domain names (e.g. WHOIS data), and enriching log data with infrastructure information based on the cloud provider.
A big part of that enrichment is only made possible if the SIEM solution subscribes and imports additional data sources, such as IP blacklists and 3rd party security feeds. These feeds are extremely important and often dictate the effectiveness of the SIEM solution, therefore having quality built-in feeds from cybersecurity vendors and other organizations is crucial.
From the next generation of SIEM solutions we need to expect nothing less than meaningful alerts that leave little to interpretation. A solution capable of using AI and Machine Learning algorithms to power analytics combined with strong security knowledge will have a clear advantage.
The traditional and old school SIEM solutions relied on static thresholds to produce alerts, which causes fatigue and quite often useless alerts and false positives. Although there were improvements like somewhat dynamic thresholds, this only reduced false positives, but left the company open to more attacks.
Instead, by leveraging machine learning algorithms coupled with expert security knowledge, a modern SIEM solution will learn from the behavior and natural patterns of a system and users and only alert you true causes for concern.
In fact, User and Entity Behaviour Analytics, or simply UEBA, is nowadays one of the must-have capabilities for a next-generation SIEM.
UEBA, a term coined by Gartner a few years back is the concept of detecting anomalous behavior of users and machines against a defined normal baseline behavior. Profiling the user of a given system is incredibly helpful. As an example, one could expect that a machine or system used by a Developer can execute several PowerShell commands in a given period of time, while the same exact behavior from a machine used by someone working in Marketing would be very suspicious.
Similarly, the entity (i.e. machine) profiling is equally important. If a machine that is usually only used during working hours suddenly initiates network connections (e.g. VPN) to a distant remote location at 4 AM is a strong indicator that something is wrong and likely to raise suspicion.
The evolution of SIEM solutions has been nothing short of remarkable. A major driver has been as mentioned above cloud computing, both with the technology innovations and developments that it gave us but also the inherent security challenges.
As you move forward in developing your existing SIEM capabilities or adopting a whole new solution, it is very important to choose a solution that brings true value to the organization and provides you actionable intelligible alerts and recommendations. As we covered in this article, scalability and good integration capabilities with the 3rd party systems and data sources your organization has are key, as is the information enrichment, intelligence, adopting the UEBA concept combined with security expertise.
Want to read more about security? There is a lot more on our blog, including this article on AWS Security. Check it out!