The Security Trifecta: Operationalizing API Protection with AWS, Wallarm, and Coralogix
In the modern digital world, API’s are no longer just “connectors” – they are the real security product. Whether you are a Fintech processing payments, a SaaS platform managing multi-tenant data, or an E-Commerce giant handling the bulk of sales, your API’s are the foundation of your customer registration, checkout experiences, and partner ecosystems.
However, that transition has made API’s the fastest-growing attack surface in history.
While many organizations have invested in a standalone WAF, a SIEM or basic/advanced perimeter controls, API incidents continue to skyrocket. What is the reason? Security operations remain fragmented. Attacks are detected in one silo, investigated in another, and mitigated through a slow, manual coordination between security, engineering and DevOps teams. To solve this, a new “Security Trifecta” has emerged: AWS for resilient infrastructure, Wallarm for deep API protection, and Coralogix as the operational glue.
For years, the industry treated WAF and API Security as separate conversations. Today, that separation is a liability. WAF is your perimeter shield; it stops the “noisy” attacks – DDOS, SQL Injection, and known/unknown malicious IP’s. API security, however, is about context and logic. It identifies threats that appear to be valid traffic but are actually malicious or vulnerable, such as an attacker trying to access another user’s data (BOLA) or scraping a product catalogue via an authenticated session.
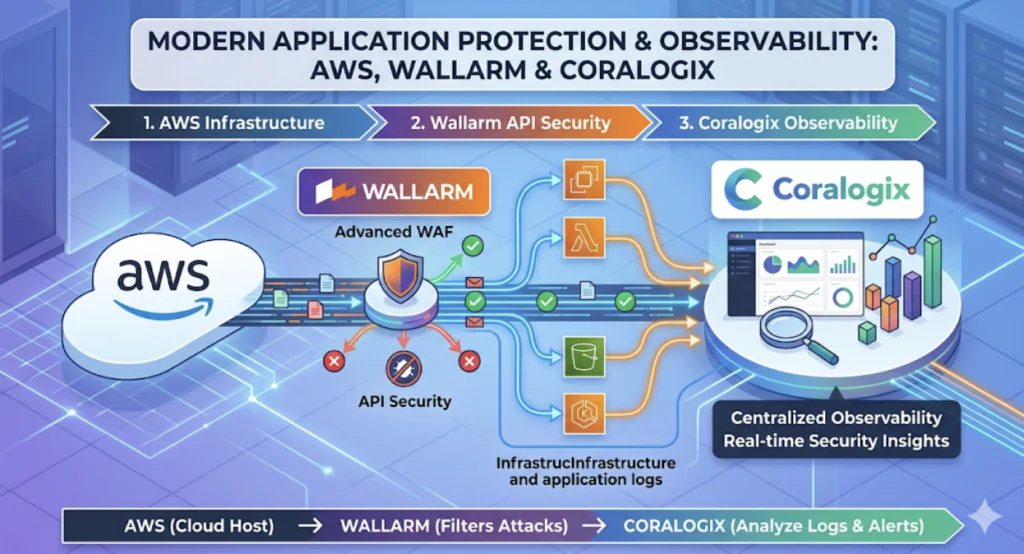
The link between the two is critical: the WAF filters the “obvious” bad actors at the edge, while API security deep-dives into the “internal” logic of the call. Without both, you are either overwhelmed by noise or blind to sophisticated breaches. The partnership among AWS, Wallarm, and Coralogix represents a shift toward modern, secure infrastructure and deployment. Instead of bolting security on as an afterthought, this stack integrates security into the very fabric of the cloud :
AWS – provides the high-availability infrastructure – EKS, Lambda, CloudFront, etc. – where modern applications live. By using Infrastructure as Code (IaC), organizations can deploy security at the same speed as their features. The partnership ensures that security isn’t a bottleneck but an automated part of the CI/CD pipeline.
Wallarm – provides high-fidelity API threat detection. It doesn’t just look for signatures; it understands API protocols (gRPC, GraphQL, REST) and identifies business logic abuse. In practice, Wallarm answers the most vital question: “Is this specific API traffic malicious?”
Once an alert is triggered, the clock starts ticking. This is where Coralogix transforms a simple alert into actionable intelligence. By sitting at the intersection of security and observability,
Coralogix correlates Wallarm’s detections with:
- Infrastructure Logs: What happened at the AWS network level?
- APM Traces: Which microservices were touched by this request?
- Real-Time Metrics: Is the attack causing a spike in 5xx errors or latency?
The necessity of this integrated approach is best exemplified by the gaps found in recent major hacks:
- LinkedIn breach – reported incident harvesting 700M records, missing API logic-based protection. The missing API security gap: In several recent high-profile “scraping” breaches, attackers used authorized API keys to slowly harvest millions of user records. A traditional WAF saw “valid” traffic and stayed silent. Only an API Security solution would have flagged the abnormal object-level enumeration.
- The missing SIEM/correlation gap: In the recent Okta breach (breach of its customer support unit), attackers used stolen session tokens to move laterally. Because the signals were scattered across different logs, it took weeks to realize a breach had occurred. Coralogix acts as the glue, correlating identity logs with application behaviour to spot session hijacking in real-time.
- UnitedHealth breach missed perimeter/WAF gap (catastrophic ransomware attack cost). Many ransomware attacks begin with simple credential stuffing on unprotected endpoints. A robust WAF integrated with AWS infrastructure can stop these volumetric attacks before they ever reach the API layer.
For modern enterprises, this trio delivers more than just “security” – it delivers a “must-have” business requirement and outcomes:
- Faster triage (MTTD/MTTR): no more manual log-hunting. Coralogix enriches Wallarm alerts with AWS environment tags.
- Reducing alert fatigue: by correlating detections with actual system impact (Response, Errors and Duration), SOC teams only focus on attacks that are actually succeeding.
- Unified ownership: Security and R&D teams finally have a shared “source of truth.” Security sees the threat, while engineering sees the affected trace.
Wallarm brings the detection, AWS brings the scale, and Coralogix brings the intelligence. Together, it enables a modern API security posture that isn’t just accurate, but operational.