FortiGate Firewall – Top 10 Best Practices

FortiGate Next-Generation Firewall utilizes purpose-built security processors and threat intelligence services to deliver protection and high performance, including encrypted traffic inspection. FortiGate reduces complexity with automated visibility into applications, users, networks, and security-rated traffic to ease the implementation burden.
The importance of getting the firewall configurations right cannot be overstated. This guide describes the top 10 best practices that you can use to improve FortiGate security posture. These best practices help ensure the optimal performance, security, and stability of their FortiGate firewall and network infrastructure.
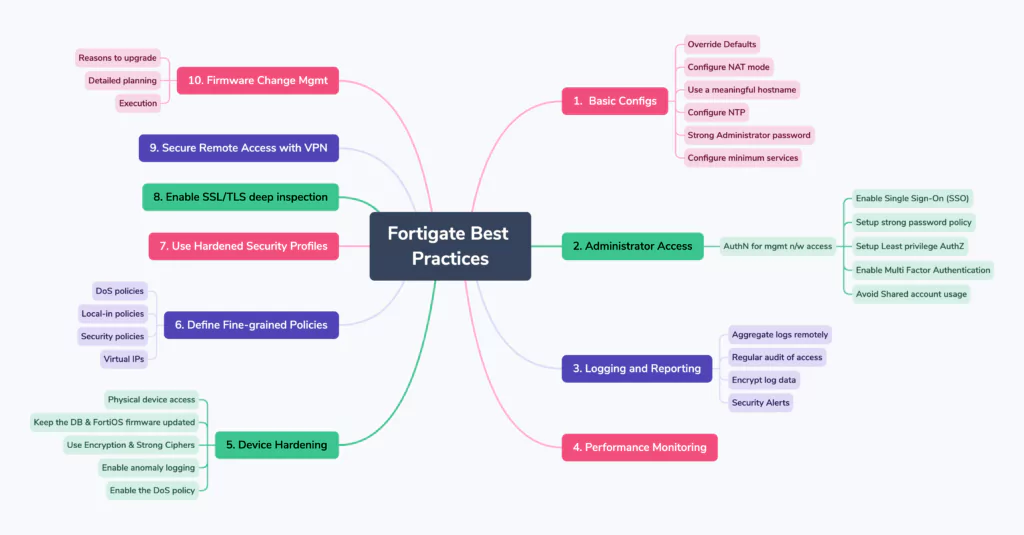
Here is a brief visual overview of the guidelines we will discuss in this post:
Basic Configuration
As soon as FortiGate is connected to the internet it is exposed to external risks, such as unauthorized access, man-in-the-middle attacks, spoofing, DoS attacks, and other malicious activities from malicious actors.
Below are the general guidelines or considerations when setting up a FortiGate firewall:
- Override Defaults – Either use the start-up wizard or manual reconfiguration to change the default settings and tighten security.
- Configure NAT mode – For granting cross zone access i.e. from less secure zone to more secure zone, NATed IP addresses should be used so traffic can be monitored easily.
- Use a meaningful hostname – Giving your FortiGate firewall a meaningful hostname (which is used in the CLI prompt as the SNMP system name, as the FortiGate Cloud device name, and as the device name in an HA configuration) allows you to easily identify and differentiate it from other devices on your network. This can be helpful, especially in larger network environments..
- Configure NTP – Use a Network Time Protocol (NTP) or Precision Time Protocol (PTP) server to set the system time. Synched-up time helps in detective control by piecing the information together accurately.
- Use Strong Administrator password – The administrator password must be set when you first log in to FortiGate. Ensure that the password is unique and has adequate complexity.
- Configure minimum services – Configure the IP address, subnet mask, and only the required administrative access services (such as HTTPS and SSH) on the management interface.
Learn more here.
Administrator Access
Give special attention to management traffic that is accessing the FortiGate. There are 3 different ways Administrative Access can be managed –
- Utilization & Configuration of Management Network
- Strong user AuthN/AuthZ for Management Network Access
- Hardening Administrative settings
Management Network
There are many benefits to using a management network for administrative access to your network devices:
- Reliability:
When management traffic is independent from production or business traffic, it does not have to compete for resources and therefore is less at risk of losing access when reconfiguring the production network. - Simpler policies:
Using a management interface allows for policy separation of the management and production traffic. Policies with specific purposes are easier to understand and troubleshoot. - Security:
It is more difficult for bad actors to access network devices on the production network when their management access is on a separate network.
A single interface or VLAN interface in the management network should be dedicated to all administrative access. Administrative access should be disabled on all other interfaces.
Note: Avoid using the WAN interface, or a publicly exposed interface, for management, as it will be subject to constant attacks.
User Authentication for management network access
The least privilege access principle should be used for controlling access to FortiGate. The following are recommendations for accessing FortiGate:
- Enable Single Sign-On (SSO) – FortiGate firewalls support Single Sign-On (SSO) capabilities, which can greatly simplify the authentication process for users across various network resources. FortiGate integrates with popular SSO protocols such as Security Assertion Markup Language (SAML), Lightweight Directory Access Protocol (LDAP), and Active Directory (AD).
- Setup strong password policy – For local accounts on the FortiGate, define a password policy to ensure a minimum complexity level.
- Setup least privilege authorization – The features that an administrator can access should be limited to the scope of that administrator’s work to reduce possible attack vectors.
- Regular audit of user access – The list of users with access should be audited regularly to ensure that it is current.
- Consider whitelisted client IP schema – Trusted hosts can also be used to specify the IP addresses or subnets that can log in to the FortiGate administration interface.
- Enable Multi-Factor Authentication – When authenticating in FortiGate, implement multi-factor authentication (MFA). This makes it significantly more difficult for an attacker to gain access to the FortiGate.
- Avoid Shared account usage – Do not use shared accounts to access the FortiGate. Shared accounts are more likely to be compromised, are more difficult to maintain as password updates must be disseminated to all users, and make it impossible to audit access to FortiGate.
Administrative Settings
The following general administrative settings are recommended:
- Idle timeout – Set the idle timeout time for administrators to a low value, preferably less than ten minutes.
- Usage of Non-Standard port – Use non-standard HTTPS and SSH ports for administrative access.
- Disable weak encryption protocols – Do this as much as possible on a regular basis.
- Utilize trusted certificates – Replace the certificate that is offered for HTTPS access with a trusted certificate that has the FQDN or IP address of the FortiGate.
Logging and Reporting
Logging generates system events, traffic, user login, and many other types of records that can be used for alerts, analysis, and troubleshooting.
- Aggregate logs remotely – All FortiGate events should be logged & logging records should be stored securely. It is advised to send the log to a central location to account for device failure or other unforeseen events.
- Encrypt log data – Due to the sensitivity of the log data, it is important to encrypt data in motion/at-rest through the logging transmission channel. Communication with FortiAnalyzer and FortiCloud is encrypted by default.
- Logging into third-party devices – This should be done over secure channels. In the event, channel security cannot be assured a VPN on the remote logging device can be utilized before transmitting logs to it -.
- Enable FortiAnalyzer log option – Logging options include FortiAnalyzer, syslog, and a local disk. Logging with syslog only stores the log messages. Logging to FortiAnalyzer stores the logs and provides log analysis, hence should be utilized.
- Security Alerts – Once your logs are flowing into a central location which could be a Security information and event management (SIEM) system, you can setup detection rules or alerts. Setting up FortiGate detection alerts is crucial for several reasons:
- Early threat detection
- Timely incident response
- Mitigating advanced threats
- Compliance requirements
- Incident investigation and forensics
- Proactive security posture
See here for more details.
Performance Monitoring
It is very important to monitor the performance of your device. FortiGate supports multiple protocols for monitoring resource utilization, such as SNMPv3, NetFlow, and sFlow. These protocols are used to measure the performance of the FortiGate and provide insight into the traffic that it is passing.
Resource monitoring helps establish resource utilization baselines that can be useful for:
- Configuring IPS signature rates.
- Recognizing abnormal activity, such as when an attack is occurring.
- Comparing the bandwidth utilization over specific time spans, such as month to month or year to year, to plan for growth.
- Comparing the bandwidth utilization between different WANs, and applying SD-WAN and traffic shaping as needed.
- Tuning security profiles to optimize resource usage.
You can use WAN Optimization & Cache widgets to confirm that a FortiGate unit is optimizing traffic and view estimates of the amount of bandwidth saved.
Device Hardening
System hardening reduces security risk by eliminating potential attack vectors and shrinking the system’s attack surface.
Some of the best practices described previously in this document contribute to the hardening of FortiGate with additional hardening steps listed here:
- Secure physical device access – Install FortiGate in a physically secure location. Physical access to FortiGate can allow it to be bypassed, or allow other firmware to be loaded after a manual reboot.
- Keep the FortiOS firmware up to date – The latest patch typically has the most bug fixes and vulnerability fixes, making it the most stable version..
- Use of Encryption – Utilize encrypted protocols whenever possible. For example:
- LDAPS instead of LDAP
- RADSEC over TLS instead of RADIUS
- SNMPv3 instead of SNMP
- SSH instead of telnet
- OSPF MD5 authentication
- SCP instead of FTP or TFTP
- NTP authentication
- Encrypted logging instead of TCP
- Enable only strong ciphers – Force higher levels of encryption and strong ciphers. Strong crypto is enabled by default.
- Update Fortiguard DB – Ensure that FortiGuard databases, such as AS, IPS, and AV, are updated continuously and have the most updated definitions at all times.
- Trust but verify – Test your FortiGate to try to gain unauthorized access, or hire a penetration testing company to verify your work.
- Enable anomaly logging – When enabling anomaly logging keep the action as ‘monitor’ for some time. This is to observe and understand what expected traffic looks like so that you may tune thresholds to have small margins, and therefore more protection. Keep note of false alarms. If they are too frequent, you should adjust your policy accordingly.
- Enable the DoS policy – Enable the DoS policy anomalies to help prevent targeted attacks.
- Utilize custom private Key – To enhance password security, specify a custom private key for the encryption process.
- Backup your configurations – There are many reasons to backup your configuration, such as disaster recovery, preparation for migrating to another device, and troubleshooting.
Defining fine-grained Policies
Use different policy types to secure the different types of traffic that FortiGate processes, to control fine-grained control over network traffic. For example:
- DoS policies
- Local-in policies
- Security policies
- Virtual IPs
See here for more details.
Hardening Security Profiles
Security profiles define what to inspect in the traffic that FortiGate is passing. When traffic matches the profile, it is either allowed, blocked, or monitored (allowed and logged).
- Assess policy & traffic match – Apply the necessary level of protection after assessing policy & traffic matching
- Consider DoS security policies – This helps detect and drop illegitimate traffic before it reaches the more resource-intensive security profiles (see Denial of service for more information).
- Apply flow mode inspection – Do this for policies that prioritize traffic throughput, and apply proxy mode when thoroughness is more important than performance.
Learn more here.
Enable SSL/TLS deep inspection
TLS encryption is used to secure traffic, but the encrypted traffic can be used to get around your network’s normal defenses.
Enable SSL/TLS deep inspection to inspect traffic even when they are encrypted.
See here for more details.
Securing Remote access
The number of remote workers is increasing, and networks are expanding into thin branch networks and the cloud. Secure remote access is advancing to meet the requirements of increasingly distributed environments.
Assess your requirements and review the available options to determine the solution that best meets your requirements.
Fortinet has IPsec and SSL VPN options. SSL VPN has two modes: tunnel and web.
See here for more details.
Firmware Change Management
Consider the following points when performing firmware upgrades, not only in FortiOS but as general rules for any change you have to make in a production environment:
- Understand the new version
- Have valid reasons to upgrade the firmware
- Prepare a detailed plan
- Take business and technical aspects into consideration
- Execute the upgrade as per the planning
Note: FortiGate, and its service contract, must be registered to have full access to Fortinet Customer Service and Support, and FortiGuard services. FortiGate can be registered in either the FortiGate GUI or the FortiCloud support portal. The service contract can be registered from the FortiCloud support portal.
See here for more details.
Out-of-the-Box Fortigate Security with Coralogix’s Snowbit
So far we have discussed best practices about how to secure Fortigate. Equally important is to have in place mechanisms to be notified in real-time of any unusual or abnormal events and/or configuration changes. Hence detective controls must be in place.
Coralogix’s Snowbit security offering provides a comprehensive set of out-of-the-box detections & alerts for Fortigate. Some of the notable ones include:
- Multiple login failures
- Anomalous denied actions (by source, destination)
- Malicious IP address OR DNS name detected based on threat intelligence indicators
- Unwanted or malicious applications detected
- Possible data leak prevention events detected
Not only are existing alerts customizable based on specific customer requirements but also any needed custom detections and dashboards can be added quickly by our team – reducing time to value dramatically.
We would love to discuss this further with you, so feel free to schedule a demo with our team.