Managing OpenTelemetry at Scale: Why OTel Pipelines Need a Control Plane
OpenTelemetry made telemetry possible everywhere – turning observability pipelines into distributed production infrastructure. Distributed infrastructure requires a control plane for inventory, governance, and safe change.
At 500 collectors across hybrid environments, operational overhead becomes a production risk. The moment telemetry pipelines become a distributed infrastructure, they inherit the operational problems of one.
The Reality of Day-2 Operations
When teams move past initial deployment into long-term maintenance, they encounter the consequences of unmanaged infrastructure:
- Velocity bottlenecks: Updates require repeated PRs, Helm upgrades, staged restarts, and manual verification. This manual cycle is too slow for modern DevOps.
- Coverage blindspots: Finding outdated or non-reporting environments takes manual investigation, leaving gaps in instrumentation.
- Noisy neighbors: Misconfigured collectors quietly consume CPU and memory. Without fleet-wide visibility, these outliers are hard to detect and remediate consistently.
Left unaddressed, these operational pains become significant consequences for the business:
- Configuration drift leads to inconsistent telemetry and security postures across the cloud environment.
- Slow, manual rollouts create long compliance windows during active incidents.
- Waiting hours for PRs and Helm upgrades to propagate a configuration fix extends MTTR and stalls troubleshooting when every minute counts.
- Without a centralized inventory, teams simply cannot answer critical questions about which versions or configurations are running in specific environments.
Ultimately, this reliance on manual changes results in a massive operational impact for every update.
Teams need the same rollout control and governance for observability pipelines that they already expect from Kubernetes and CI/CD.
In practice, that means a control plane that can:
- Give you a live inventory of what’s running and whether it’s healthy
- Enforce version consistency and highlight drift
- Target changes safely (canary → phased rollout → full rollout)
- Prove convergence and keep an audit trail (and rollback when needed)
Coralogix Fleet Management provides that control plane for OpenTelemetry at scale.
What Fleet Management Is (and Why OpAMP Matters)
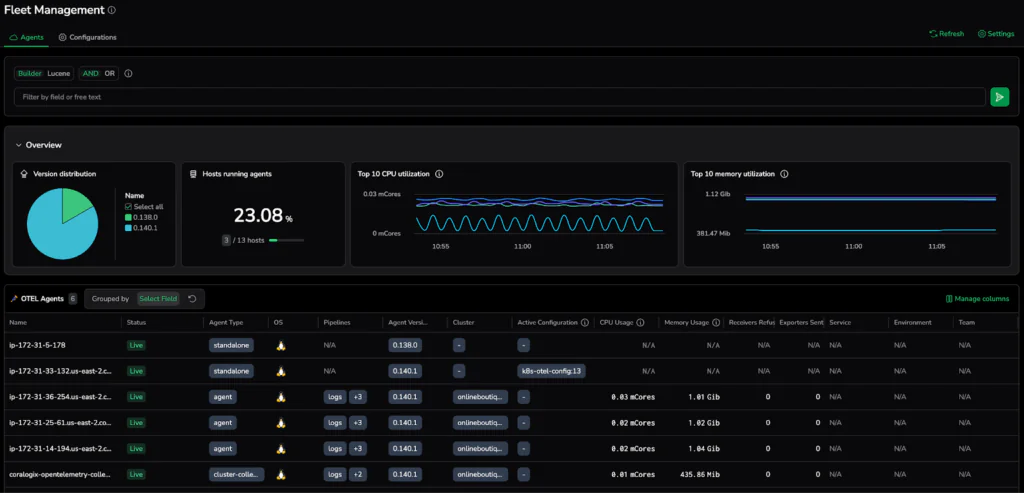
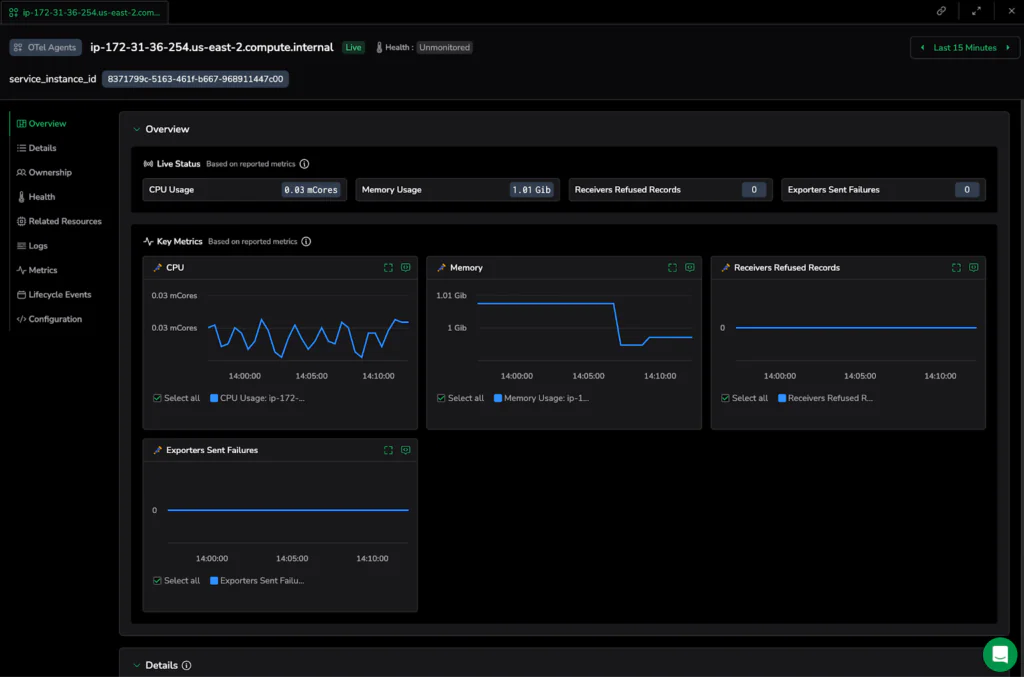
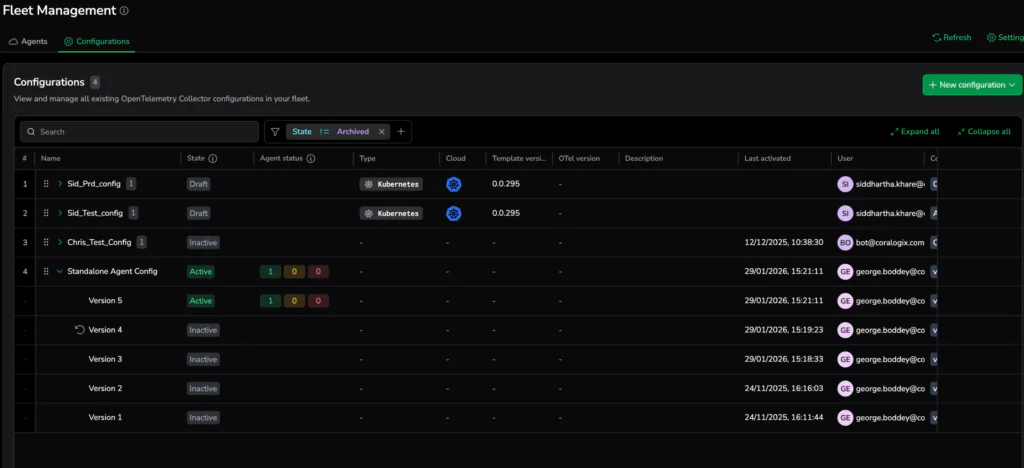
Fleet Management acts as the control plane for OpenTelemetry, giving teams centralized visibility into collector health, versions, and resource usage across their fleet.
Concretely, the control plane shows up in two places:
- Fleet-wide inventory and health view (so you can see what’s running and spot drift/outliers)
- Controlled rollout mechanism (so configuration changes become targeted, observable deployments – not manual work per cluster).
Inventory & health (Agent Catalog): Centralized operational visibility into agent health, versions, and resource footprint – so you can find outliers and gaps without manual investigation.
Controlled change (Supervisor-enabled remote configuration): A supervised mechanism to deliver approved configuration updates and restart collectors so configuration rollouts are repeatable, targeted, and auditable.
To ensure this control plane remains open and vendor-agnostic, the system utilizes OpAMP (Open Agent Management Protocol). This standardizes the communication between the management plane and your agents, ensuring consistent orchestration.
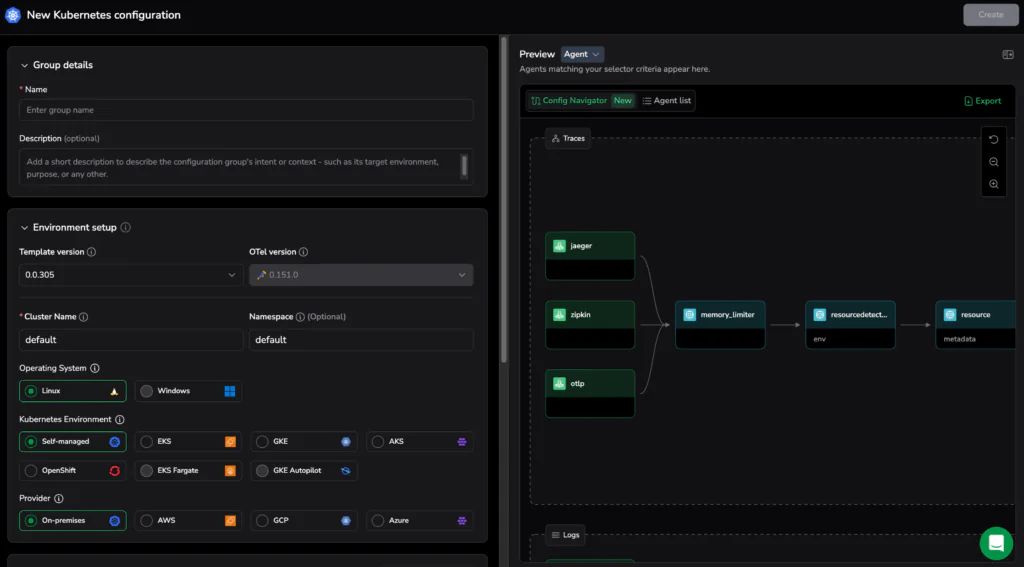
The Architecture: Remote configuration is made possible by the OpenTelemetry Supervisor, which manages each Collector instance. The interaction follows a secure, structured flow:
- Standardized Communication: The Supervisor establishes an HTTP connection to the Fleet Management interface.
- Update checks (OpAMP HTTP transport): Because we utilize the OpAMP HTTP transport, the Supervisor regularly checks in with the management plane to receive approved configuration updates.
- Automated Configuration Delivery: Once a change is detected, the Supervisor retrieves the update, applies it, and automatically restarts the Collector to activate the new configuration.
Real-World Impact: The Security Redaction Scenario
To understand the value of a telemetry control plane, let’s consider a scenario: a security audit identifies exposed PII in your telemetry, requiring an immediate redaction configuration update across every OTel pipeline in your organization.
This is a major hurdle. Organizations often struggle to implement PII redaction across hundreds of collectors, leading to fragmented policies where some data is missed entirely. Without orchestration, these shifts are slow, inconsistent, and prone to error.
Before: The Manual Marathon
In a traditional, unmanaged setup, pushing a security update follows a grueling, manual path that mirrors the slow pace of legacy infrastructure management:
- The PR Bottleneck: Create and merge Pull Requests for multiple Helm charts across dozens of namespaces and clusters.
- The Waiting Game: Manually trigger upgrades and wait for pods or services to restart across every environment.
- The Validation Gap: Log into multiple systems to verify that the new configuration is active, then manually validate that the resulting telemetry is actually being redacted.
- The Compliance Window: Throughout this hours-long process, misconfigured collectors remain active, leaving a window where sensitive data continues to leak into your backend.
After: Orchestrated Fleet Rollouts
With Fleet Management, this operational loop is compressed into a single, auditable workflow.
Step 1: Before making a change, use the Agent Catalog to verify your fleet’s current state. This centralized visibility shows which versions are active and identifies outliers that require specific attention.
Step 2: Targeted Precision (Selectors) instead of “bulk update and pray” approaches isolate specific hosts or clusters, allowing for safe canary rollouts where you test redaction logic on a subset of agents before a global push.
Step 3: Preview and activate a coordinated config set (Configuration Family) to ensure Agent, Gateway, and Cluster Collector configs stay synchronized. The UI provides a built-in preview so you can see which agents match the selectors before activation.
Step 4: Monitor Rollout Health as the Supervisor retrieves the new configuration during its next update check. You can monitor the rollout status as it converges across the fleet. If a collector fails to apply the configuration, you can drill down into its diagnostics to pinpoint the bottleneck and resolve it immediately.
Orchestration is the New Standard
The emergence of OpenTelemetry solved telemetry generation. The next operational challenge to overcome is telemetry governance at scale. Observability pipelines are more distributed than ever, so infrastructure organizations need the same deployment safety, visibility, and lifecycle control they already expect from Kubernetes and CI/CD systems.
Coralogix Fleet Management turns telemetry changes from manual infrastructure work into controlled, observable deployments. It ensures that as your OpenTelemetry footprint grows, your operations remain consistent, audited, and scalable.
Take Control of Your Fleet
If you are ready to move from manual configuration to automated fleet orchestration:
- Audit Your Inventory: In Coralogix, navigate to Integrations → Fleet Management to view your Agent Catalog and identify version gaps or health outliers.
- Enable Remote Configuration: Deploy your collectors with the Supervisor enabled to unlock versioned rollouts and centralized configuration management in the Configurations tab.
Get Started with Coralogix Fleet Management