CDN Logs – The 101 Guide
A Content Delivery Network (CDN) is a distributed set of servers that are designed to get your web-based content into the hands of your users as…
Auth0 is one of the top leading identity management platforms in the world. It’s focused on providing solutions for application builders, specifically solutions needed for custom-built applications. Auth0 provides expertise to scale and protect identities in any application, for any audience. This post will show you how Coralogix can provide log monitoring, analytics and insights for your Auth0 log data – including performance and security insights.
Auth0 generates system events related to the authentication activity of your users. The data provides an audit trail that helps you understand activities within your platforms. Each log event object describes a single logged action or “event” performed by a certain actor for a certain target and its result.
You can leverage this event data by using Coralogix alerts and dashboards to instantly detect problems and their root causes, spot malicious behavior, and get real-time notifications on any event you can define. Ultimately, this offers a better monitoring experience and more value out of your Auth0 data with minimal effort.
To connect your Auth0 logs with Coralogix you will first need to send your Auth0 events to Amazon EventBridge and route them to AWS CloudWatch and then, send them from CloudWatch to Coralogix with our predefined Lambda function.
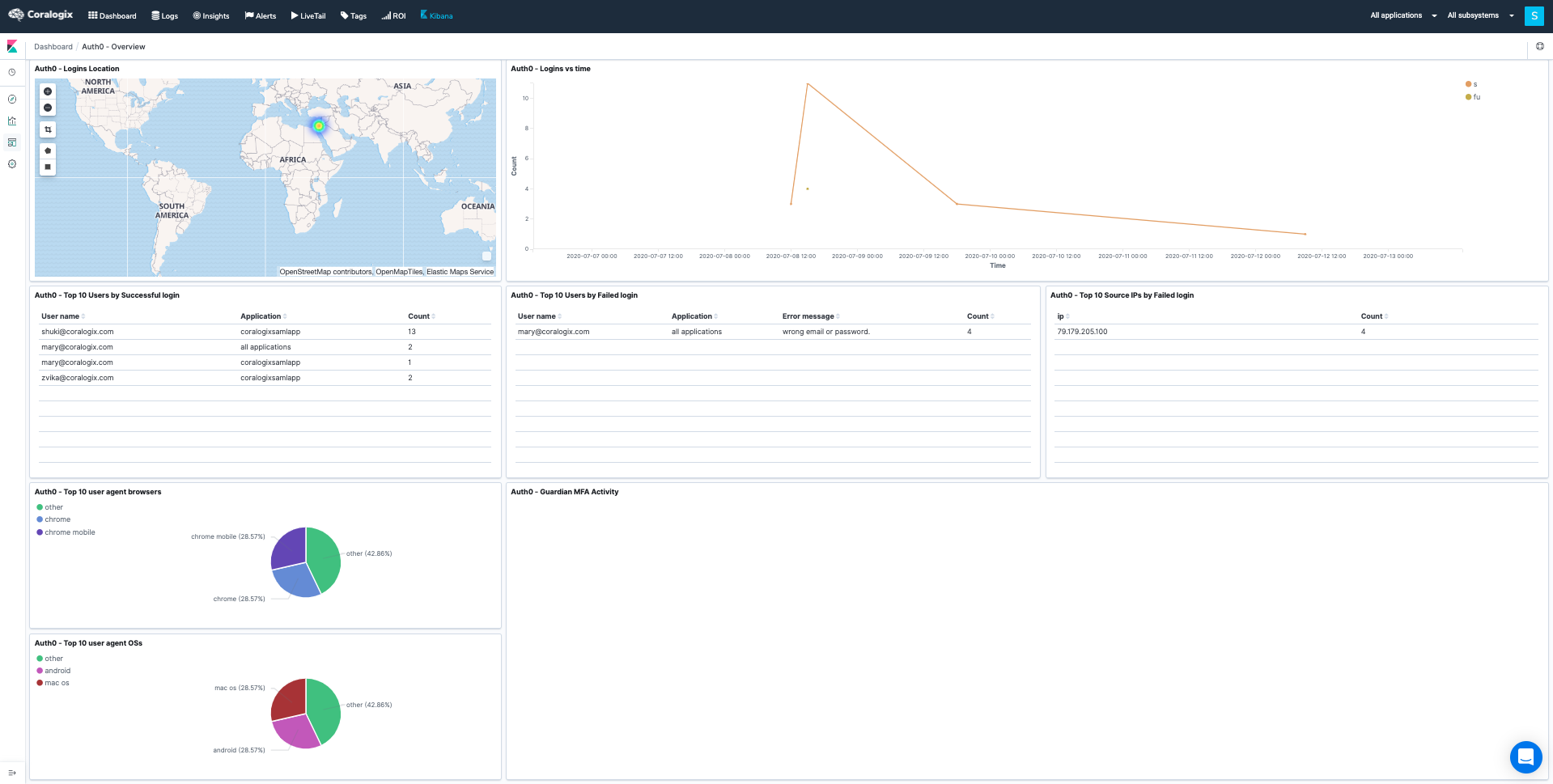
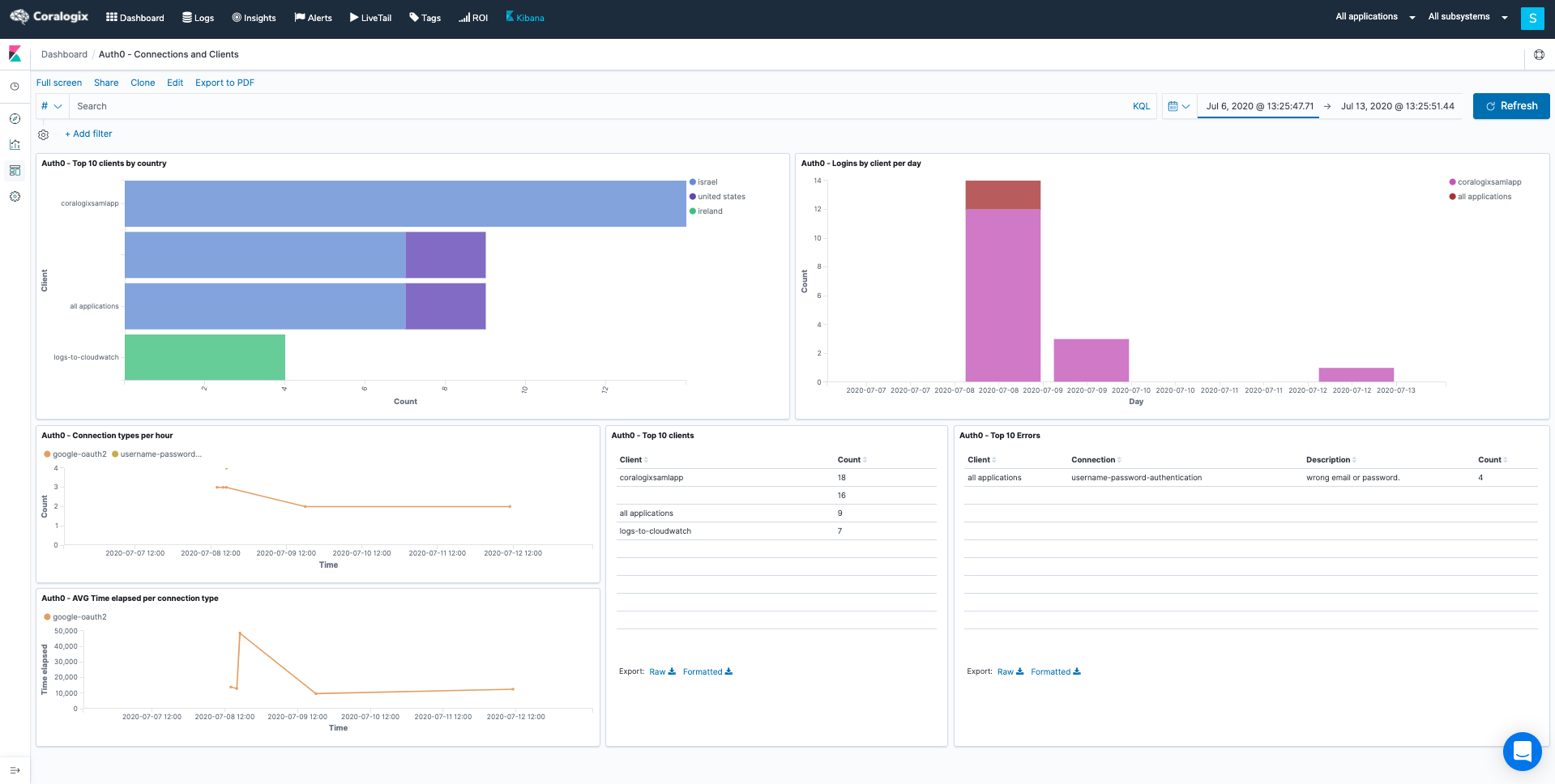
Here are a few examples of Kibana dashboards we created, using the Auth0 log data, Coralogix IP address GEO enrichment, and Elastic queries.
You may create additional visualizations and dashboards of your own, using your Auth0 logs. For more information on using Kibana, please visit our tutorial.
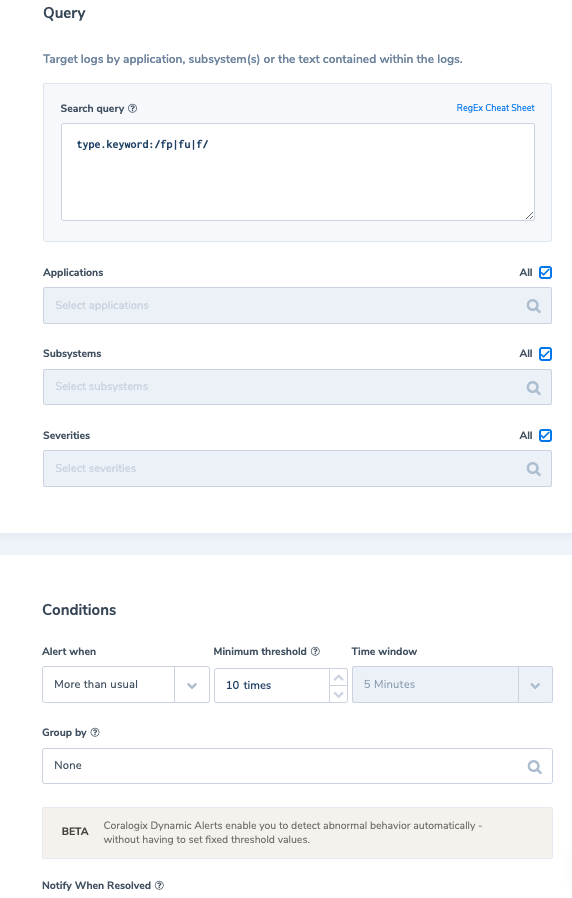
Coralogix User-defined alerts enable you to easily create any alert you have in mind, using complex queries and various conditions heuristics, thus being more proactive with your Auth0 logs with insights you couldn’t gain or anticipate from a traditional log investigation. Here are some examples of alerts we created using traditional Auth0 log data.
Alert Filter: type.keyword:/fp|fu|f/
Alert Condition: ‘More than usual times, within 5 min with a minimum of 10 occurrences’.
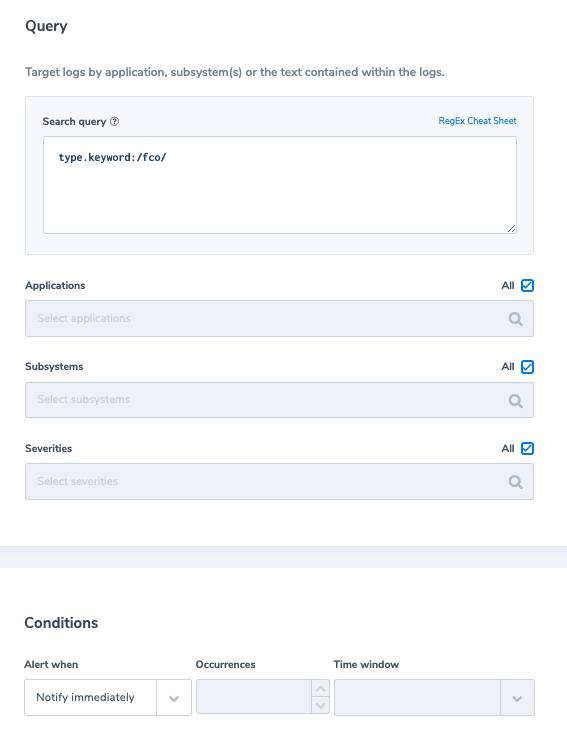
Alert immediately if an application request Origin is not in the Allowed Origins list for the specified application.
Alert Filter: type.keyword:/fco/
Alert Condition: ‘Notify immediately’
Alert Filter: type.keyword:/s/ NOT ip_geoip.country_name:(israel OR ireland OR “united states”)
Alert Condition: ‘Notify immediately’

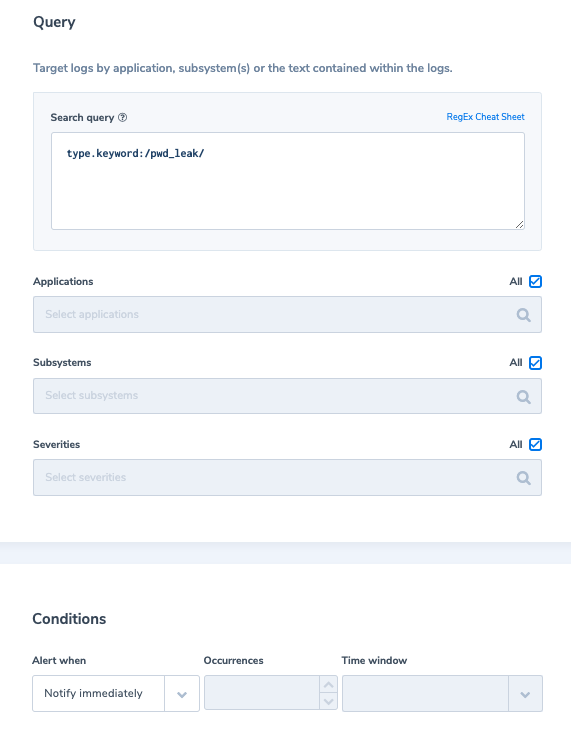
Someone behind the IP address: IP attempted to log in with a leaked password.
Alert Filter: type.keyword:/pwd_leak/
Alert Condition: ‘Notify immediately’
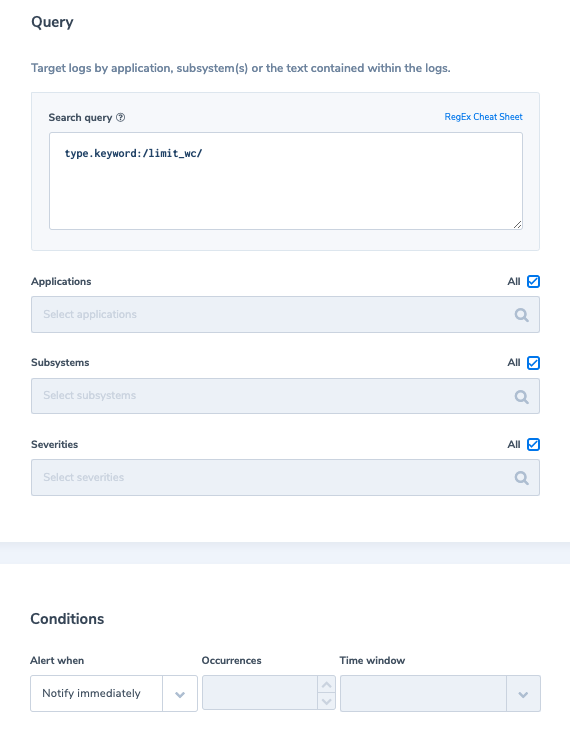
An IP address is blocked with 10 failed login attempts into a single account from the same IP address.
Alert Filter: type.keyword:/limit_wc/
Alert Condition: ‘Notify immediately’
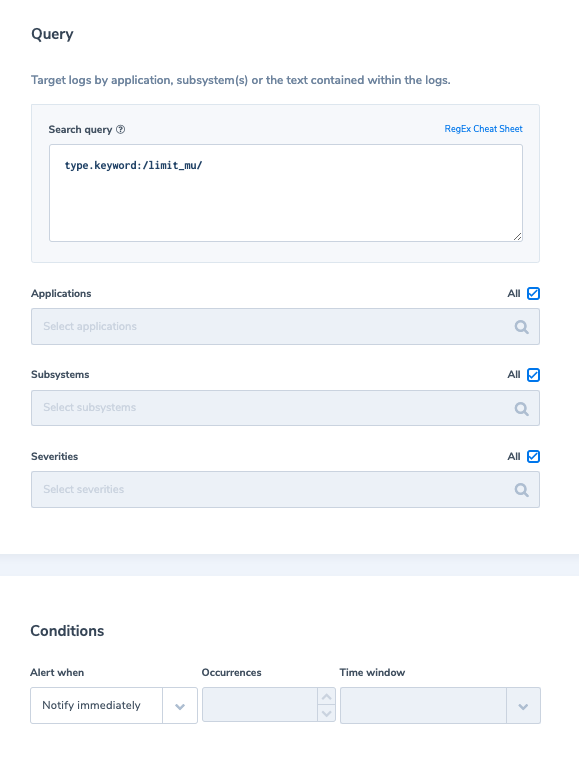
An IP address is blocked with 100 failed login attempts using different usernames, all with incorrect passwords in 24 hours, or 50 sign-up attempts per minute from the same IP address.
Alert Filter: type.keyword:/limit_mu/
Alert Condition: ‘Notify immediately’
Need More Help with Auth0 or any other log data? Click on the chat icon on the bottom right corner for quick advice from our logging experts.